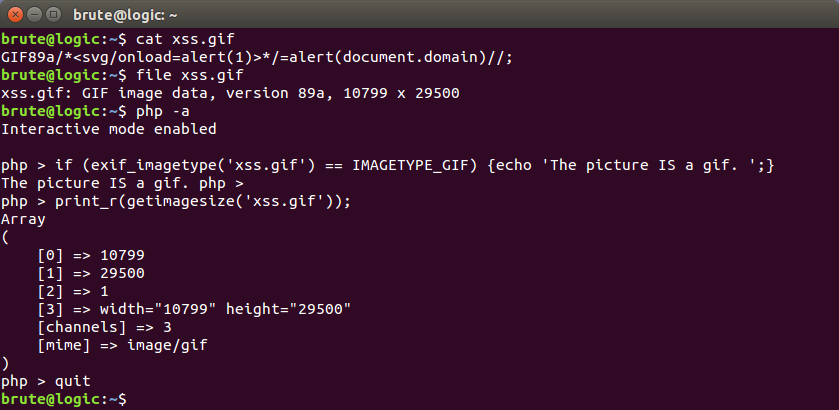
16+ Svg File Upload Xss PNG. A file upload is a great opportunity to xss an application. Let's assume that a website has a file upload function. Most people assume svg files are image files in the same way as png or gif, but really they are xml files which describe an image. Does the threat of xss exists when loading an untrusted svg file using the img tag? Failed to load latest commit information. If this happens you can attempt to upload a svg file as your profile picture or something else and when you view this file your xss payload will execute. The functionality of file upload is a key place where we should pay special attention to. You're right about the script being able to run if you open the file locally, but it can't really do much in that environment. Javascript's same origin policy prevents it from accessing any cookies or other sensitive. #hack2learn although not intended, it's possible to. Currently assessing an application, i found out that it is possible to submit an svg file containing javascript (the app is also vulnerable to xxe). I wondered if there was a method to prevent those vulnerabilities and secure the svg submission form? Intuitively scalable vector graphic is a vector graphic that defines the image with shapes instead of the colors of individual groups of pixels. What kind of files we should be given a special treatment? User restricted area with an uploaded profile picture is everywhere, providing more chances the filename itself may be being reflected in the page so it's just a matter of naming the file with a xss.
Download 16+ Svg File Upload Xss PNG SVG Cut File